About Veson
We are Veson Nautical
And we’re on a mission to transform the way the maritime world works and makes decisions through the power of technology.
Veson Nautical is a global market leader in developing, implementing, and supporting the solutions that propel maritime commerce.
We deliver the best commercial platform on the market, but we aren’t just a technology company. We are a digital transformation company. Driven by a commitment to continual innovation, a spirit of collaboration, and an unwavering focus on client success, Veson is a trusted partner to our clients as they navigate new possibilities in a digital age.
Our Vision
To be the standard platform that propels maritime commerce.
Fast Facts
38,000+ Global Users
Presence in 75+ Countries
6 Global Centers of Excellence
200+ Maritime Technologists & Professionals
Our Values
These are the principles that propel us.
Do the right thing.
For clients, for colleagues, for community.
Take pride in your work.
Drive quality, raise the standard.
Move forward.
Collaborate, innovate, deliver.
Our Story
Learn about our dynamic 20-year history and evolution as a leader in maritime shipping digitalization.

Our Solutions
Our dynamic suite of products are transforming the way the world’s shipowners, operators, tonnage charterers, and commodities traders work and make decisions. Discover how our robust capabilities can bring value to your business.
Your Career
Our team is rapidly growing in all regions of the world. We are looking for bright, purpose-driven professionals that share our commitment to excellence. Sound like a good fit?

This isn’t about our success.
It’s about yours.
Enough talking about us. We prefer to talk about our clients. Our clients include the world’s largest vessel owners, operators, commodities traders, and tonnage charterers. Together, they represent a substantial piece of global trade. Our favorite thing to do is enable them to be even more successful.












Our Locations
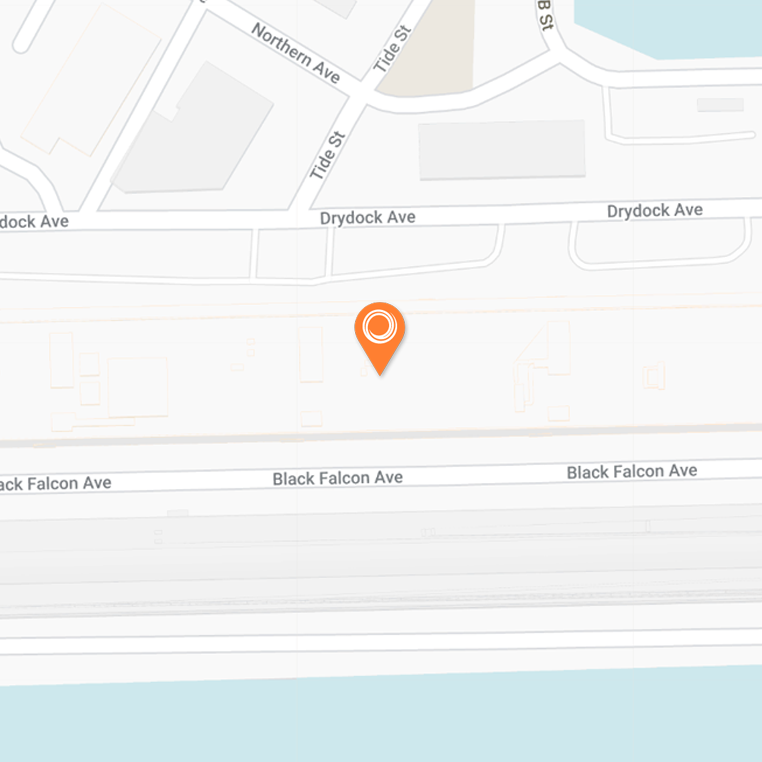
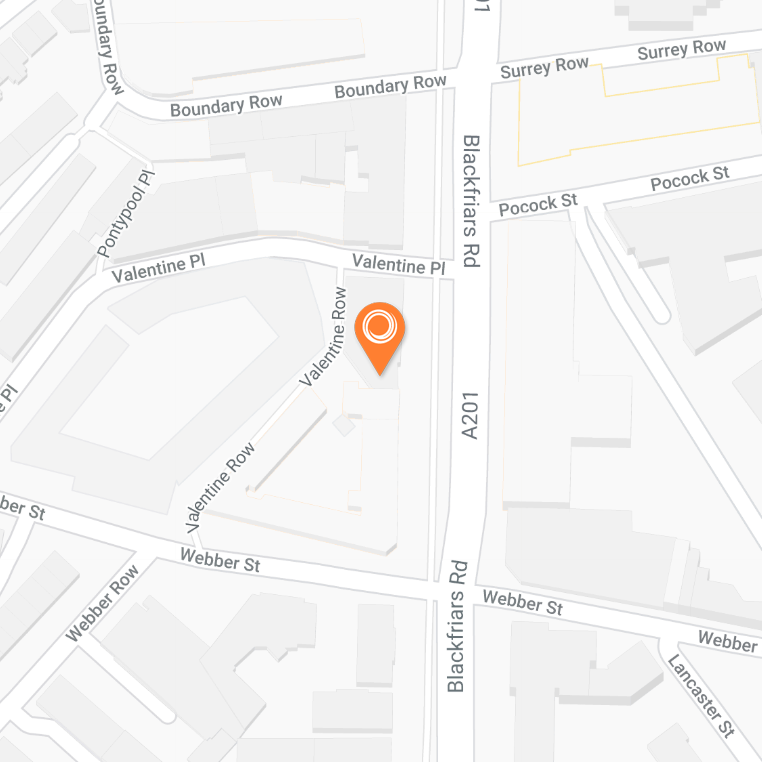
Veson Nautical
21 Drydock Avenue, Suite 610W
Boston, Massachusetts 02210
United States
Tel: +1.617.723.2727
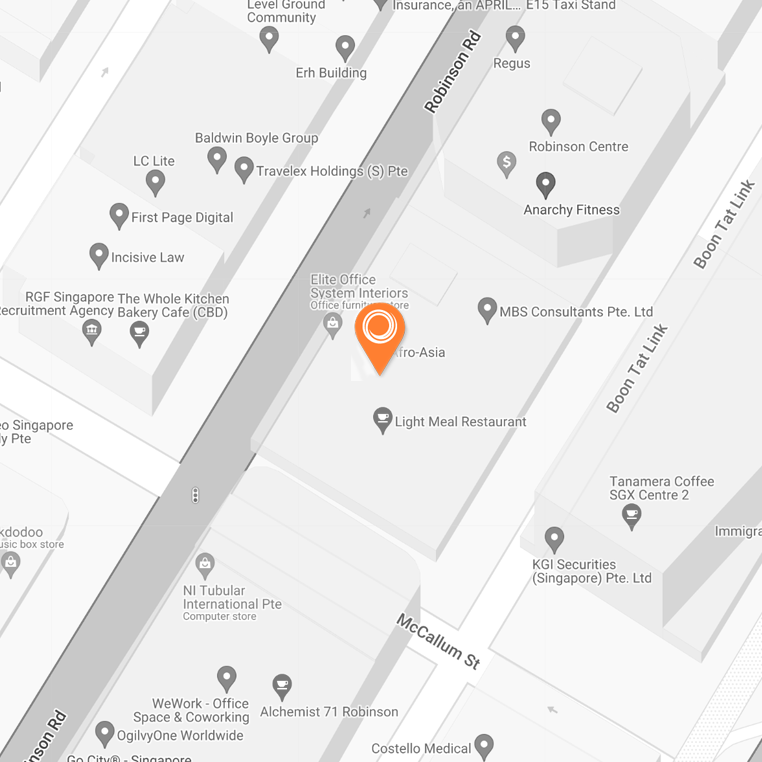
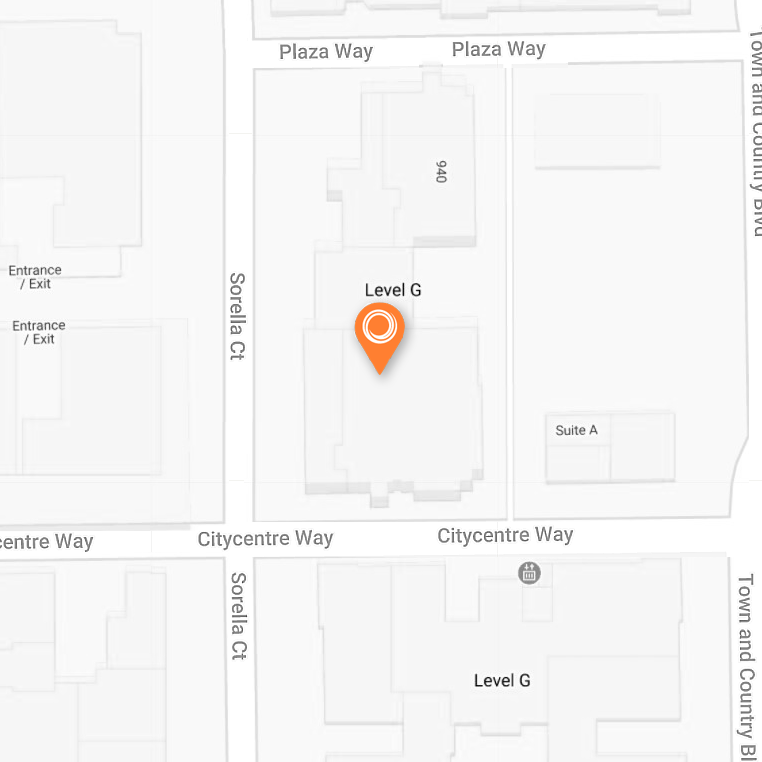
Veson Nautical PTE LTD
63 Robinson Road, Afro Asia #17-01
Singapore, 068894
Singapore
Tel: +65.6225.4881

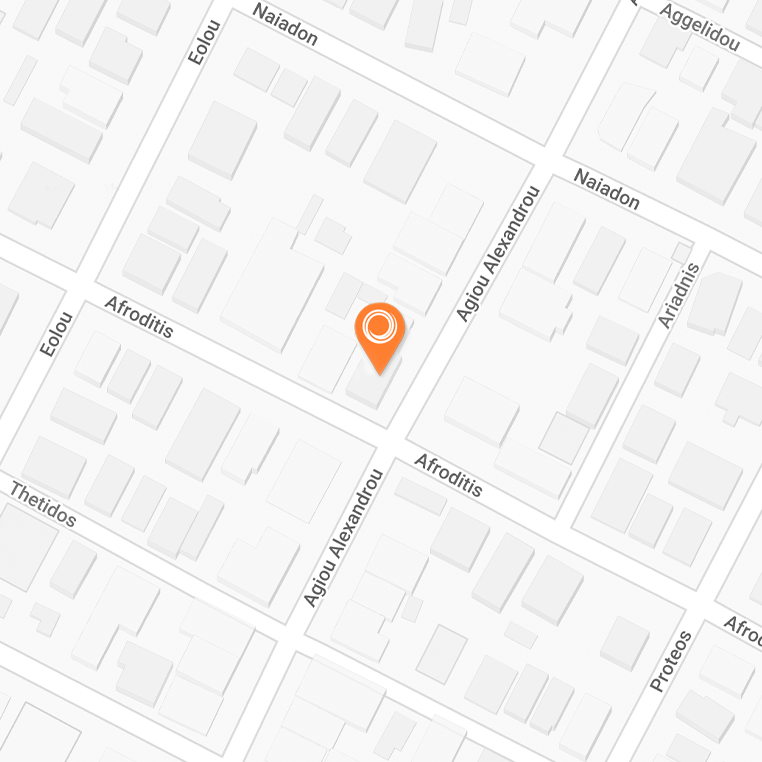
Veson Nautical Japan GK
Fukoku Seimei Bldg 15F, 2-2-2,
Uchisaiwai-cho, Chiyoda-ku,
Tokyo 100-0011, Japan
Tel: +81.3.4571.2220
Connect with us
Participate in the conversation that is shaping the bright, digital future of maritime commerce by following us on social media.
Looking for more info? Email info@veson.com to learn more.
Ready to begin your digital journey?
Veson can help you embrace change and maximize ROI. Discover the power of our proven partnership.